VAPT Explained: Vulnerability Assessment & Penetration Testing in 2026
VAPT — Vulnerability Assessment and Penetration Testing — is the controlled, deliberate version of what attackers do uncontrolled. VAPT — Vulnerability Assessment and Penetration Testing — is the controlled, deliberate version of what attackers do to you uncontrolled.
1. What is VAPT, in One Paragraph?
VAPT is a structured security assessment that combines two complementary techniques. Vulnerability Assessment (VA) systematically identifies and catalogues weaknesses across an asset. Penetration Testing (PT) attempts to exploit those weaknesses, chain them together, and measure real-world impact. Together they answer two questions: what is wrong and how badly can it actually hurt us.
2. VA vs. PT: The Difference That Matters
- VA is broad and largely automated — scanners (Nessus, Qualys, OpenVAS) sweep an asset and produce a long list of CVE-tagged findings. Cheap, fast, scales easily.
- PT is narrow and human — a tester picks the most promising findings, attempts exploitation, pivots, escalates, and demonstrates business impact. Expensive, slow, irreplaceable.
- You need both. VA without PT misses the chained 3-step attack that turns three “medium” findings into one “critical” data exfiltration. PT without VA misses easy wins and wastes tester time.
Useful test for vendors: if their “VAPT” output looks identical to a Nessus export, you bought VA, not VAPT. Demand to see proof-of-exploitation screenshots and chained attack paths.
3. Types of VAPT (and When You Need Each)
- Web Application VAPT — OWASP Top 10 + business-logic testing. Required for any externally-exposed app handling user data.
- Mobile App VAPT — static + dynamic testing of Android (APK) and iOS (IPA) builds, including reverse engineering, runtime hooking (Frida), and backend API testing.
- API VAPT — OWASP API Top 10. The most under-tested asset in 2026 — APIs accumulate quietly while testing focuses on the visible web app.
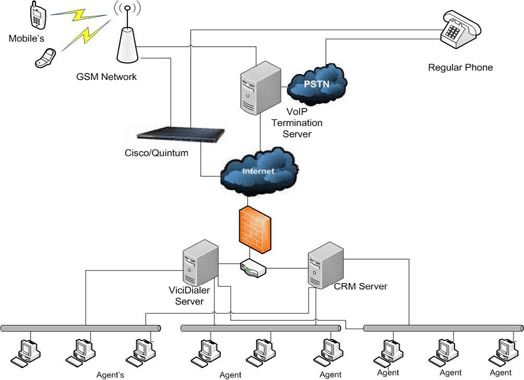
- Network VAPT — internal and external network. Catches misconfigured services, exposed admin panels, weak authentication.
- Cloud testing — AWS / Azure / GCP configuration review against CIS benchmarks; IAM analysis; serverless and container testing.
- IoT / OT the engagement — firmware analysis, hardware interfaces, radio protocols. Niche but essential for healthcare, manufacturing, and critical infrastructure.
4. The Engagement Lifecycle: From Scoping to Remediation
A defensible engagement runs through six phases:
- Scoping & Rules of Engagement (ROE) — assets in scope, off-limits actions, contact tree, working hours, data-handling clauses.
- Reconnaissance — passive (OSINT, DNS, certificate transparency) and active (port scans, service fingerprinting).
- Vulnerability Identification — automated scans + manual review.
- Exploitation — attempt controlled exploitation of high-confidence findings; chain where possible.
- Post-exploitation — privilege escalation, lateral movement, data-access proofs (without exfiltration).
- Reporting & Remediation Validation — written report with executive summary, technical detail per finding, remediation guidance, and a re-test pass after fixes.
5. Tools of the Trade in 2026
- Web/API: Burp Suite Professional (still the standard), Caido (rising challenger),
ffuf,nuclei, OWASP ZAP for automation. - Network:
nmap,masscan, Nessus / Qualys, Metasploit Framework, Impacket suite for AD work. - Mobile: Frida + Objection, MobSF for static analysis, Burp + a rooted/jailbroken test device.
- Cloud: ScoutSuite, Prowler, CloudSploit, Pacu for AWS attack simulation,
kubescapefor Kubernetes. - Reporting: Dradis, PlexTrac, or templated Markdown — the tool matters less than the discipline of consistent severity ratings.
6. Compliance Frameworks That Mandate VAPT
- PCI-DSS 4.0: requires both internal and external pen testing at least annually and after significant changes.
- ISO 27001:2022: requires regular technical compliance reviews — this testing is the standard implementation.
- RBI / SEBI guidelines: Indian banks, NBFCs, and regulated financial services require periodic engagements with CERT-In empanelled auditors for critical systems.
- HIPAA / HITECH: requires regular technical evaluation of safeguards.
- SOC 2: auditors expect annual penetration testing as evidence of the CC7 control series.
7. How Often Should You Do VAPT?
The default cadence we recommend:
- External web/API: at least annually, plus after every major release.
- Mobile apps: annually + before major store releases.
- Network (internal + external): annually.
- Cloud: continuous via posture management; deep testing annually.
Continuous discovery + targeted human testing beats one big annual report. We pair an always-on attack-surface monitoring service with quarterly focused engagements for clients who can resource it.
8. Choosing a Testing Partner: 7 Questions to Ask
- Are your testers OSCP / OSWE / CRTP / CEH-Practical certified, and can you share resumes?
- Will you do manual exploitation, or only run automated scans? Can I see a redacted sample report?
- What is your methodology — OWASP, NIST SP 800-115, PTES?
- How do you handle high-impact findings discovered mid-engagement (out-of-band notification)?
- Is a re-test included after we remediate?
- What is your data handling policy for findings, screenshots, and credentials?
- Are you CERT-In empanelled (relevant for Indian regulated entities)?
Pair this with our broader cybersecurity services review and you will dodge the worst categories of vendor.
Frequently Asked Questions
How long does a typical web application engagement take?
For a mid-sized web app with authentication, role-based access, and ~50 endpoints, plan 8–12 working days for testing plus 3–5 working days for reporting. Larger apps with many user roles can run to 20+ days.
Black-box, grey-box, or white-box — which should we choose?
Grey-box (authenticated tester, no source) hits the best cost-to-coverage ratio for most clients. Black-box mirrors a real external attacker but misses authenticated bugs. White-box (with source) finds the most depth but is the most expensive.
Is this the same as a security audit?
No. A security audit is broader and policy-focused — process, governance, documentation. security testing is specifically technical exploitation. They complement each other; a good ISO 27001 audit will recommend testing as one of the technical evidence sources.
Can this testing bring our production systems down?
Properly scoped engagement is non-destructive. Aggressive techniques (DoS testing, exploitation that requires service restart) are explicitly excluded unless you authorise them in writing. Always test against a staging mirror first if production downtime is unacceptable.
What does a good report look like?
An executive summary suitable for board reporting, a vulnerability summary table with CVSS v3.1 scores, per-finding technical detail with reproduction steps and screenshots, prioritised remediation guidance, and a clear retest section. If you cannot hand it to your dev team and have them fix things, the report failed.
How to Pick a Testing Partner That Actually Helps
The vendor market in India is crowded; the differentiation is methodology and report quality. A testing partner worth the engagement fee shows up with a kickoff agenda, a written scope, and a sample report you can read end-to-end. Skip any vendor whose deliverable looks like a Nessus export.
Further reading: OWASP Web Security Testing Guide.
Need help on something like this? VITI Security works with operators, BPOs, and SMBs across India and abroad.
Request a VAPT Scoping Call