Network Security Best Practices in 2026: Zero Trust, Microsegmentation, EDR
Network security best practices in 2026 mean abandoning the castle-and-moat model entirely. Castle-and-moat network security failed the moment your first laptop left the office.

1. Why "Castle and Moat" Failed
The classic perimeter model assumed a trusted inside and a hostile outside. That assumption breaks for three concrete reasons in 2026:
- Identity is the new perimeter. A stolen Microsoft 365 token bypasses every IP-based firewall rule you have.
- SaaS data lives outside your network. Your CRM, payroll, and source code are on someone else’s infrastructure.
- Hybrid work made every laptop a perimeter device. A compromised home router is now adjacent to your production data.
Once an attacker is inside a flat network, the median dwell time before detection is still measured in weeks. Your job in 2026 is to make that dwell time useless — to ensure that compromise of one machine cannot reach the next.
2. Zero Trust: What It Actually Means
“Zero Trust” is the most over-marketed phrase in security, but the core idea is precise: no implicit trust based on network location. Every access decision is made fresh, per request, based on identity + device posture + context.
The 3 Core Principles
- Verify explicitly. Authenticate user and device every time. MFA is table stakes; phishing-resistant MFA (passkeys, FIDO2 hardware keys) is the bar in 2026.
- Use least-privilege access. Just-in-time, just-enough. Standing admin access is a finding in any modern audit.
- Assume breach. Design as if an attacker is already inside. Microsegment, log everything, and run breach drills.
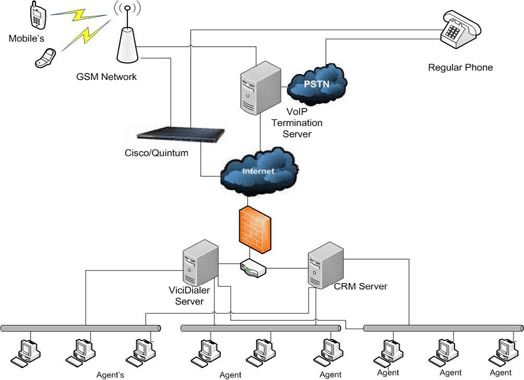
3. Microsegmentation: Containing Lateral Movement
Microsegmentation is the network-layer expression of “assume breach”. Instead of one flat 10.0.0.0/16 office network, split workloads into tight zones — each with explicit allow rules and a default-deny on everything else.
You do not need a $200k vendor to start. For most SMBs, a phased approach works:
- VLAN-level segmentation: separate user laptops, servers, IoT/printers, and guest WiFi. Block inter-VLAN traffic except whitelisted ports. Most managed switches plus a pfSense/OPNsense firewall can do this.
- Host-based microsegmentation: use Windows Firewall + group policy (or
iptables/nftablesfor Linux) to deny SMB, RDP, WinRM between user endpoints. Endpoints should never need to talk to each other directly. - Identity-aware segmentation: products like Cloudflare Zero Trust, Tailscale, or Twingate deliver application-level access without VPN — users see only the apps their identity entitles them to.
4. EDR vs. AV: The 2026 Endpoint Stack
Signature-based AV stopped being sufficient years ago. The 2026 baseline is EDR (Endpoint Detection and Response) — telemetry-rich agents that watch process trees, network connections, and registry/file events, then correlate them centrally.
What good EDR looks like for an SMB:
- Behavioural detections, not just hashes — catches living-off-the-land attacks (PowerShell, WMI, scheduled tasks).
- Auto-isolation: when a host hits a high-confidence detection, the EDR cuts its network access in seconds.
- 30+ day telemetry retention, searchable by your responders.
- Managed detection (MDR) tier — a 24/7 SOC reviewing alerts, because an SMB cannot staff that internally.
If you cannot pay for one tier of MDR, you cannot afford to skip it. Unattended EDR alerts are noise; investigated EDR alerts are protection.
5. Building a Practical Zero-Trust Stack on a SMB Budget
For a 50–250 person Indian SMB, here is a realistic stack we recommend in 2026:
- Identity: Microsoft Entra ID or Google Workspace, with conditional access + phishing-resistant MFA enforced.
- EDR/MDR: CrowdStrike Falcon Go, SentinelOne Singularity, or Microsoft Defender for Business with a managed SOC partner.
- Network: Fortinet FortiGate or pfSense Plus at the perimeter; managed L2/L3 switches with VLANs; UniFi or Mist for WiFi with separate SSIDs.
- Remote access: Cloudflare Zero Trust or Tailscale — replaces full-tunnel VPN.
- Email: Microsoft Defender for Office 365 P1, plus DMARC/DKIM/SPF enforcement.
- Logging: ship to a SIEM — Wazuh, Elastic Security, or Microsoft Sentinel for organisations already in M365.
6. Implementation Roadmap (90 Days)
What our team typically delivers in three months:
- Days 1–14: Asset inventory, identity audit, MFA enforcement on all admin accounts, EDR rolled out to 100% of endpoints.
- Days 15–45: VLAN segmentation, firewall rules tightened to default-deny, perimeter logging into the SIEM, phishing-resistant MFA piloted with executives.
- Days 46–75: Host-based microsegmentation policies, conditional access on all SaaS, remote access migrated off legacy VPN.
- Days 76–90: Tabletop ransomware exercise, written incident response plan, recovery test of the most critical backup.
7. Compliance: DPDP, ISO 27001, and the Insurance Question
India’s Digital Personal Data Protection Act (DPDP), 2023, took effect in stages through 2025. By 2026, “reasonable security safeguards” is no longer hand-wavy — auditors expect documented controls equivalent to ISO 27001 Annex A or NIST CSF. The good news: the zero-trust architecture above maps almost 1:1 onto the controls you will need to evidence.
Cyber-insurance underwriters now demand EDR, MFA on all admin accounts, and offline-immutable backups before they will quote — make sure your stack ticks those boxes when you renew.
Frequently Asked Questions
Do I really need to throw out my existing firewall to do zero trust?
No. Your perimeter firewall stays — zero trust extends inward, not outward. You add identity-aware access for users and microsegmentation between workloads. The firewall keeps doing its perimeter job; you stop relying on it as your only layer.
Is microsegmentation realistic for a 50-person company?
Yes, in phases. Start with VLAN-level segmentation between users, servers, and IoT — that alone blocks most ransomware lateral movement. Host-based and identity-aware segmentation come later. The cost is configuration time, not new hardware.
Free Defender vs. paid EDR — what is the actual difference?
Microsoft Defender Antivirus is good signature/heuristic protection. Microsoft Defender for Endpoint (paid) adds the EDR telemetry, behavioural detections, and centralised investigation that lets you respond to incidents. For DPDP/ISO compliance and cyber-insurance, the paid tier is effectively required.
How do we measure that zero trust is working?
Three signals: (1) mean time to detect (MTTD) drops as logging and EDR improve; (2) blast radius of red-team exercises shrinks — a compromised laptop should reach near-zero other systems; (3) audit findings on standing privilege and shared credentials trend to zero.
What is the single highest-ROI control to implement first?
Phishing-resistant MFA on every privileged account, paired with conditional access. It blocks the majority of credential-theft chains that lead to ransomware — usually within a single afternoon of work.
Network Security Best Practices: What Actually Survives 2026
Network security best practices in 2026 share three properties: identity-first authorisation, default-deny lateral movement, and continuous logging that someone actually reviews. Network security best practices for Indian SMBs do not require six-figure tooling — they require a documented inventory, MFA enforcement, EDR rollout, microsegmentation, and a tabletop exercise once a quarter. Every network security best practices engagement we run in 2026 starts with the same gap analysis and ends with the same control set. The differentiator is consistent execution, not novel tooling.
Further reading: VITI Security cybersecurity services · NIST SP 800-207 Zero Trust Architecture.
Need help on something like this? VITI Security works with operators, BPOs, and SMBs across India and abroad.
Book a Network Security Audit