Post-Quantum Cryptography in 2026: Practical Migration for Indian Enterprises
Post-quantum cryptography migration is no longer "future planning" — by 2026 it is an active engineering project. A working quantum computer that breaks RSA is still years away — but the data being encrypted today is the data that will be decrypted tomorrow.
Post-Quantum Cryptography: What NIST Actually Standardised
In August 2024, NIST released the first three finalised post-quantum cryptography (PQC) standards: FIPS 203 (ML-KEM) for key encapsulation, FIPS 204 (ML-DSA) for digital signatures, and FIPS 205 (SLH-DSA) as a stateless hash-based backup signature scheme. A fourth, FIPS 206 (FN-DSA / Falcon), followed in 2025. Vendor implementations rolled out through 2025; by 2026 most modern TLS stacks support hybrid PQC key exchange behind a feature flag.
The standards are public and stable: NIST CSRC PQC project, FIPS 203.
Why You Need to Care in 2026 (Even If You Don't Touch Defence Data)
The “harvest now, decrypt later” threat is the immediate concern. Adversaries — both nation-state and organised crime — are already capturing encrypted traffic on the assumption it will be decryptable inside a 10–20 year window once cryptographically-relevant quantum computers exist.
Anything you encrypt today that has long-lived secrecy value is at risk: trade secrets, M&A documents, source code, customer data with identification value, regulatory filings. For Indian financial-sector firms operating under RBI guidance and the DPDP framework, the exposure window for personal data is 7+ years; for healthcare records, longer. The decision to migrate is not driven by quantum timelines — it is driven by the data’s sensitivity horizon.
A Realistic Post-Quantum Cryptography Migration Roadmap for 2026
The migration is not “rip and replace”. The mainstream pattern is hybrid: classical + PQC together, so that traffic is safe even if either algorithm is broken.
- Inventory. Map every place you use cryptography — TLS, VPN, code-signing, email signing, document signing, hardware security modules, internal authentication. Tooling:
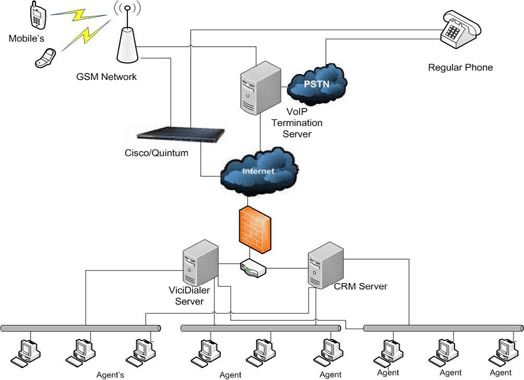
nmap --script ssl-enum-cipherson perimeter, plus internal-asset crypto inventory via configuration-management tools. - Pick one high-value, low-risk target. Most Indian enterprises start with TLS termination on the public-facing CDN/load-balancer layer in hybrid mode (X25519+ML-KEM-768). Cloudflare, Akamai, and AWS ALB all support hybrid as of 2025.
- Crypto agility upgrades for code-signing. SLH-DSA is the conservative pick for software signing because it is hash-based and structurally simpler. Plan a 12-month roll for any product distribution chain.
- HSM and PKI. Hardware vendors (Thales, Entrust, Utimaco) shipped PQC firmware updates through 2025. Issuing a parallel root with PQC algorithms is the standard pattern; legacy-cert reissue follows over 24 months.
- Vendor pressure. Demand a PQC roadmap commitment in renewal RFPs for SaaS, identity providers, and HSM vendors.
Sector-Specific Notes for India
- BFSI (RBI / SEBI): RBI has not yet issued binding PQC guidance, but the CERT-In advisories of late 2025 reference PQC migration as a “recommended planning activity” for critical sector entities. Expect formal guidance through 2026–2027.
- Critical infrastructure: Aligning with NIST timelines is the safe planning baseline; Indian critical-sector regulators tend to follow within 1–2 years of NIST publication.
- SaaS exporters: If you sell to US federal customers under FedRAMP or FedRAMP+, PQC alignment is on the FedRAMP roadmap and will land as a control before most customers ask.
Common Post-Quantum Cryptography Migration Pitfalls
- Over-rotating to pure-PQC too fast. Algorithms are new; implementations are newer. Hybrid first.
- Forgetting embedded systems. IoT and OT devices on 5–15 year refresh cycles will be the hardest assets to migrate. Inventory now.
- Treating PQC as an “infosec project”. It is a cross-functional engineering project. Application teams, identity teams, infra teams, and supply chain teams all need representation.
FAQ
When will quantum computers actually break RSA?
Honest answer: nobody knows. Public roadmaps from IBM, Google, and Quantinuum suggest a cryptographically-relevant quantum computer within 10–25 years. The migration timeline matters more — your data’s 10-year confidentiality window is what drives the decision today.
Should we deploy pure PQC or hybrid?
Hybrid for at least the next 3–5 years. Combining classical and PQC algorithms means the connection is secure if either algorithm holds. Pure-PQC deployment makes sense once the implementations have years of production scrutiny.
Does TLS 1.3 already include PQC?
The TLS 1.3 specification did not originally include PQC, but the IETF defined hybrid key-exchange groups (e.g., X25519+ML-KEM-768). All mainstream browsers and CDNs ship support behind feature flags as of early 2026. Server-side configuration is the gating step for most deployments.
Is SLH-DSA worth it given the larger signature size?
For long-lived signatures (code signing, document archival), yes — SLH-DSA is hash-based and structurally conservative. For high-volume real-time signing (TLS, JWT), ML-DSA is the practical choice.
Why Post-Quantum Cryptography Migration Cannot Wait
Post-quantum cryptography migration is a multi-year cross-functional engineering project, not an infosec patch. Indian BFSI, healthcare, and SaaS operators with long-confidentiality data should start the post-quantum cryptography inventory in 2026 — every TLS endpoint, code-signing chain, document-archive system, and HSM has a migration path. Hybrid post-quantum cryptography (X25519 + ML-KEM-768 in TLS) is the practical first step. The cost of starting post-quantum cryptography migration in 2026 is operational; the cost of starting in 2030 is incident-driven.
Further reading: VITI Security cybersecurity services.
Need help on something like this? VITI Security works with operators, BPOs, and SMBs across India and abroad.
Plan Your PQC Migration