Bug Bounty Program Launch for a 50-Person B2B SaaS
Bug bounty program launch goes wrong for most teams in three predictable ways: cost runaway, triage overhead, and scope creep. A founding team that wanted real attacker eyes on their product — and a CFO who had heard horror stories about runaway bounty bills.
The Bug Bounty Program Launch Challenge
Three concrete worries the team named in our kickoff call:
- Cost runaway. They had budget for ~$20k of bounties in year one. They needed to spend it predictably, not blow through it on duplicates.
- Triage overhead. Their VP Engineering was the only credible triager, and they could not lose 20 hours of his time per week to bug-bounty noise.
- Scope friction. They had specific concerns about parts of the product — a billing flow, a SAML integration, a customer-data export pipeline. They did not want hunters spending hours on the marketing site.
Our Bug Bounty Program Launch Approach
We designed for narrow scope, slow opening, and tight feedback. The core decisions:
- Private invite-only on HackerOne. 12 hunters initially, hand-picked from triagers’ recommended lists. Manageable inflow.
- Scope: 4 specific subdomains only. Marketing site, status page, and docs all explicitly out-of-scope.
- Bounty table tied to CVSS, with 60–90 day visibility on tier ranges. No “pay what we feel” surprise tier.
- Triage SLA: 5 business days for first response, 14 days for severity decision. Slower than peer programs, but realistic for the team’s capacity.
- VITI Security as triage co-pilot for 90 days. We did first-pass triage; the VP Engineering only saw the filtered queue.
What We Built for the Bug Bounty Program Launch
- Scope document — 3 pages, listed in scope and out of scope assets explicitly, with named “do not test” actions (no DoS, no social engineering, no data destruction).
- ROE — testing windows, approved bandwidth limits, contact tree for high-impact findings.
- Bounty table — Critical: $2,000, High: $750, Medium: $300, Low: $75. Scope-defined bonuses (e.g., 1.5x for findings in the billing flow).
- Internal triage runbook in Notion, with severity decision flowchart and CVSS-vector worksheet.
- Slack triage channel with HackerOne integration; new submissions auto-posted, P1 findings paged the on-call engineer.
Bug Bounty Program Launch Outcomes
- 14 valid findings in 90 days: 1 critical (a SAML signature-validation bypass that would have allowed cross-tenant access), 4 high, 9 medium.
- Budget: $8,200 paid out against the $20,000 cap. The team kept the unspent budget and decided to widen scope rather than refund it.
- Triage time on the VP Engineering: averaged 2.4 hours/week, well under the 5-hour budget.
- Hunter satisfaction: median first-response time on submissions was 3.5 business days, comfortably inside the 5-day SLA.
- Promoted to public program at month 6 with widened scope and higher max bounty.
What We'd Do Differently
Our initial triage time estimate was light. We budgeted ~5 hours/week for VITI-side triage and used closer to 9 in the first month — too many submissions came in just below or just at the medium/high boundary, and the back-and-forth with hunters absorbed time. We adjusted week-five by adding a senior reviewer for borderline cases, which compressed cycles.
Second: we should have produced a hunter-facing “common pitfalls” document on day 1. Three of the early submissions were “feature, not bug” cases that the hunters could have skipped if we had documented the design choices clearly. We now ship a “Why X is intentional” appendix as part of every program-launch package.
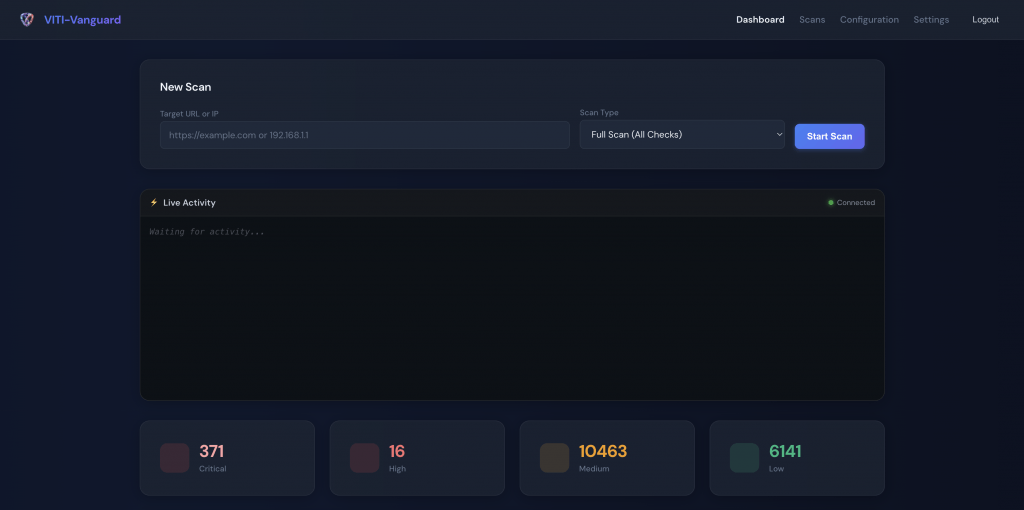
Stack & Tools
- HackerOne (private invite-only program; bounty table managed in-platform)
- Notion (internal triage runbook + severity decision flowchart)
- Slack with HackerOne integration; PagerDuty for P1 escalation
- CVSS v3.1 calculator integrated into the runbook
- 1Password for shared test-credential management with hunters
FAQ
When should a startup launch a bug bounty program?
After a real penetration test has cleared low-hanging fruit. Bug bounties are not the right tool for finding the obvious bugs — those should fall to internal review and pen tests. Bug bounties find the depth-three issues that scaled testing produces. Most teams launch too early.
Public vs. private program — which to start with?
Almost always private invite-only first. It limits inflow, lets you tune SLA and triage, and prevents the embarrassing scenario where you cannot keep up with hunter expectations on day three.
How do you set bounty amounts?
Look at peer programs (HackerOne and Bugcrowd public bounty tables), pick the 40th–60th percentile for your industry. Avoid the temptation to underpay; competent hunters check program “$ per valid find” and skip programs that under-pay relative to triage time.
How long should the first triage SLA be?
5 business days for first response is conservative and realistic for a small team. Below 3 days is hard without dedicated triage staff; above 7 days starts hurting hunter retention.
Bug Bounty Program Launch Lessons That Generalise
Most bug bounty program launch failures are scoping failures. The successful bug bounty program launch starts narrow (4 subdomains, not the marketing site), small (12 hand-picked invitees, not public day-one), and time-boxed (90-day operations support, then handoff). A well-scoped bug bounty program launch produces signal in week one and budget predictability in month one. A poorly-scoped bug bounty program launch produces inbox chaos and burnout. The decision points before launch are more important than the bounty table itself.
Further reading: VITI Security cybersecurity services · HackerOne platform.
Need help on something like this? VITI Security works with operators, BPOs, and SMBs across India and abroad.
Schedule a Program Design Session